Type: Web Article Original link: https://www.troyhunt.com/have-i-been-pwned-2-0-is-now-live/ Publication date: 2025-09-06
Author: https://www.facebook.com/troyahunt
Summary #
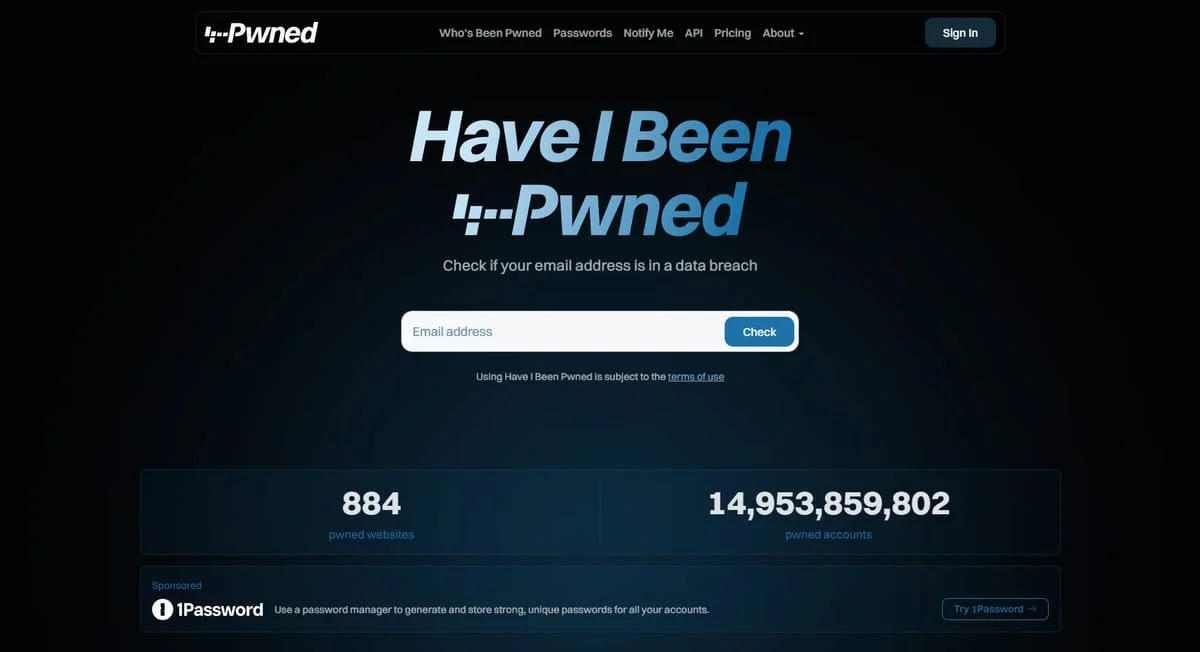
WHAT - This article discusses the launch of version 2.0 of Have I Been Pwned (HIBP), a service that allows users to check if their credentials have been compromised in a data breach.
WHY - It is relevant for AI business because information security is crucial for protecting sensitive data and preventing cyberattacks, a central issue for companies operating in the AI sector.
WHO - Troy Hunt, the creator of HIBP, is the main author. The community of users and developers who use the service are the main actors.
WHERE - HIBP is positioned in the cybersecurity market, offering tools for verifying compromised credentials. It is part of the online security ecosystem, integrating with other data monitoring and protection services.
WHEN - The launch of version 2.0 represents a significant update after a long development period. The service is established, but the new version introduces advanced features and user interface improvements.
BUSINESS IMPACT:
- Opportunities: Integration with corporate security monitoring systems to offer a compromised credential verification service to clients.
- Risks: Competition with other cybersecurity services that offer similar features.
- Integration: Possible integration with the existing security stack to enhance data protection and incident response.
TECHNICAL SUMMARY:
- Core technology stack: Uses modern web technologies such as JavaScript, TypeScript, and RESTful APIs. The backend is likely cloud-based and serverless.
- Scalability: The service is designed to handle a high volume of requests, using cloud technologies to scale dynamically.
- Technical differentiators: The new version introduces a customizable dashboard, a dedicated page for each breach with specific advice, and a merchandise store. The removal of username and phone number searches simplifies the user interface and reduces data parsing complexity.
Use Cases #
- Private AI Stack: Integration into proprietary pipelines
- Client Solutions: Implementation for client projects
- Strategic Intelligence: Input for technological roadmap
- Competitive Analysis: Monitoring AI ecosystem
Resources #
Original Links #
- Troy Hunt: Have I Been Pwned 2.0 is Now Live! - Original link
Article recommended and selected by the Human Technology eXcellence team, processed through artificial intelligence (in this case with LLM HTX-EU-Mistral3.1Small) on 2025-09-06 10:53 Original source: https://www.troyhunt.com/have-i-been-pwned-2-0-is-now-live/
Related Articles #
- Improving frontend design through Skills | Claude - Best Practices, Code Review
- Claude Code is My Computer | Peter Steinberger - Tech
- Judge Rules Training AI on Copyrighted Works Is Fair Use, Agentic Biology Evolves, and more… - AI Agent, LLM, AI